In the fast-paced world of online services, having the right tools at your disposal can make all the difference. At www.vpsproxies.com, we understand the significance of seamless connectivity and security. In this blog post, we’re going to delve into the realm of API Proxy, shedding light on how they can elevate your online endeavors.
What are API proxy?
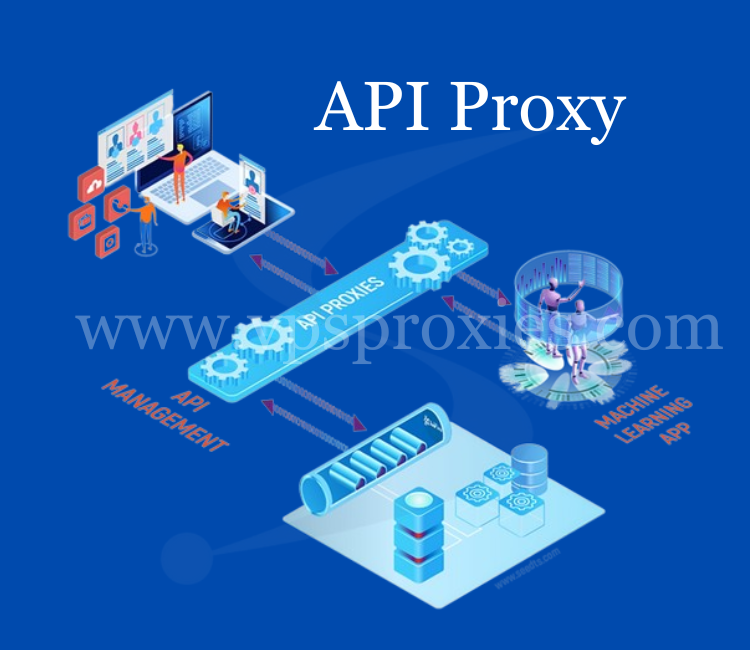
API proxies are intermediary servers or software components that facilitate communication between different software applications or systems by acting as a bridge for data exchange. These proxies play a crucial role in managing and optimizing the interaction between an application (or client) and external services, or APIs (application programming interfaces).
In simpler terms, an API proxy acts as a go-between, ensuring that requests and responses between an application and external APIs are seamless, secure, and efficient. It helps in controlling and enhancing the flow of data, adding an extra layer of functionality and security to the communication process.
How do a proxy API sever work?
API proxies work by intercepting and managing the communication between a client application and an external API (Application Programming Interface). Here’s a simplified overview of how API proxies function:
Client Sends Request:
A client application initiates a request to access data or services from an external API.
Request intercepted by the API proxy server:
Before the request reaches the external API, it passes through an API proxy. The proxy intercepts the request, acting as an intermediary.
Processing and Transformation:
The API proxy can perform various actions on the request, such as modifying headers, transforming data, or enforcing security measures. This step allows the proxy to optimize the request for the external API.
Security Measures Applied:
API proxy server often incorporate security features like authentication and encryption. Authentication ensures that the client is authorized to access the API, and encryption secures the data during transit.
Routing to External API:
After processing the request, the API proxy forwards it to the external API. The external API processes the request and generates a response.
Response Intercepted by API Proxy:
As the response travels back from the external API to the client, it passes through the API proxy again. The proxy can intercept the response for further processing.
Additional processing and transformation:
The API proxy can perform additional actions on the response, such as modifying data or headers. This step allows the proxy to tailor the response to the client’s needs
Delivery to the client:
Finally, the API proxy delivers the processed response to the client application. The client receives the data or services requested from the external API.
Key Aspects of API Proxy Functionality:
Traffic Management: API proxies can implement features like rate limiting and caching to optimize the flow of data between the client and the external API.
Monitoring and Analytics: API proxies often log information about requests and responses, providing valuable insights for monitoring, analytics, and issue resolution.
Version Control: API proxies can handle different versions of APIs, ensuring compatibility between clients and external services, even when updates or changes occur.
What are some common use cases for API proxies?
Enhancing Security:
API proxies are frequently employed to bolster the security of data transmission. By encrypting information, they ensure that sensitive details remain confidential during the exchange.
Optimizing Performance:
Additionally, proxy api play a vital role in optimizing performance. Through techniques like caching, they reduce response times, making interactions between applications and external services quicker and more efficient.
Traffic Control:
Another notable use case involves traffic management. API proxies regulate the flow of data, employing measures such as rate limiting to prevent overwhelming external services with a barrage of requests.
Cross-Origin Resource Sharing (CORS):
In scenarios where applications need to fetch data from different domains, API proxies shine in handling cross-origin resource sharing. They enable secure data retrieval from multiple sources without running into browser restrictions.
Logging and Monitoring:
Furthermore, API proxies are instrumental in logging and monitoring interactions. This continuous oversight helps identify issues, track performance metrics, and troubleshoot potential challenges seamlessly.
Version Control:
Version control is another critical aspect where API proxies prove their worth. They assist in managing different versions of APIs, ensuring smooth transitions and compatibility between evolving applications and services.
Load Balancing:
For applications dealing with varying levels of traffic, API proxies offer the advantage of load balancing. This means distributing incoming requests evenly among multiple servers, preventing any single server from becoming overloaded.
Adapting to Emerging Technologies:
As technology evolves, API proxies remain adaptable. They smoothly transition into supporting emerging technologies, ensuring that applications can seamlessly integrate new functionalities without disruptions.
Considerations when choosing an API proxy?
When selecting an API proxy, several crucial considerations come into play to ensure optimal performance, security, and compatibility. Let’s explore these key factors:
1.Security Measures:
First and foremost, assess the security features offered by the API proxy. Look for encryption, authentication mechanisms, and other security measures to safeguard your data during transit.
2.Performance Optimization:
Consider how the API proxy contributes to performance optimization. Evaluate features such as caching, which can significantly enhance response times and reduce latency.
3. Traffic Management Capabilities:
Examine the API proxies ability to manage traffic effectively. Features like rate limiting and traffic shaping can prevent overload, ensuring consistent and reliable service.
4. Cross-Origin Resource Sharing (CORS) Support:
If your applications need to interact with resources from different domains, check if the API proxy provides robust support for cross-origin resource sharing. This ensures seamless data retrieval without encountering browser restrictions.
5. Logging and Monitoring Tools:
Assess the logging and monitoring capabilities of the API proxy. Having detailed insights into interactions can aid in issue identification, performance tracking, and overall system health.
6. Version Control Mechanisms:
Evaluate how the API proxy handles version control. Ensure it supports different versions of APIs to facilitate smooth transitions and maintain compatibility as your applications evolve.
8. Ease of Integration:
Assess how easily the API proxies can be integrated into your existing infrastructure. A user-friendly integration process minimizes disruptions and accelerates the implementation of proxy services.
7. Cost and licensing structure:
Finally, examine the cost and licensing structure of the API proxy. Ensure that it aligns with your budgetary constraints and provides a clear understanding of any additional costs associated with scaling or feature usage.
Conclusion:
As you embark on your journey with www.vpsproxies.com, armed with comprehensive knowledge, you’re equipped to revolutionize your online experience. Elevate your connectivity, enhance your security, and embrace the seamless integration of cutting-edge technologies. In essence, it’s time to unlock the true potential of your online presence.